
IT Consultancy
Innovative IT Consultancy
Company in Dubai UAE
We GPC Tech Solutions-Dubai, offer full-cycle information technology consulting services to address the most daunting business challenges. From modernizing IT strategies to upgrading legacy systems to recovering software projects, we’ve got you covered all the way.
GPC Tech Solutions's IT consulting service begins with a complete understanding of the client's information technology environment & readiness for further technology upgradation, objectives and constraints. GPC Tech Solutions-Dubai, Consultants performs requirements analysis, needs assessments, system audit and then advice appropriately on IT strategic planning, Infrastructure setup, IT Security Auditing, Cloud Consulting, Software development, Technology guidance, Support and Project Management.

Business Requirements Analysis
Understanding the targeted business is the foundation for attempting to implement any IT solution for its business needs. A business requirement is what the business needs to do; what it takes to continue running the business; and what can be improved to run the business better. Business requirements analysis is a special field that covers both business and information technology (IT) worlds. Business analysts who have expertise in both business and IT are able to bridge the gap between the two worlds. The business analysts’ main tasks are:
identifying key stakeholders,
identifying key stakeholders,
understanding business process,
leading and coordinating the collection of business needs,
documenting and organizing the business process and needs,
analyzing the business needs and defining the business requirements,
and communicating the business requirements to an entire team for agreement.
IT Security auditing
We do IT security audits for the companies in Dubai. A security audits involve technical reviews reporting on configurations, technologies, infrastructure, and more. These data details that can intimidate those who feel less-than-expert in IT, but understanding the resources and strategies available to protect against modern attacks makes IT security less overwhelming.
At its root, an IT security audit includes two different assessments. The manual assessment occurs when an internal or external IT security auditor interviews employees, reviews access controls, analyzes physical access to hardware, and performs vulnerability scans. These reviews should occur, at a minimum, annually. Some organizations, however, prefer to do them more frequently. Organizations should also review system-generated reports. Automated assessments not only incorporate that data, but also respond to software monitoring reports and changes to server and file settings.
IT Security Risk Assessment Important is for any every organization
First, a risk assessment can help to justify the financial expenditures needed to guard an organization. Information security comes at a cost. Tight budgets mean that additional expenditures can be challenging to get approved. An IT security risk assessment articulates critical risks and quantifies threats to information assets. By educating internal stakeholders so they can see not only the exposure, but also the value of mitigating critical risks, a security risk assessment helps justify security investments.
Second, risk assessments help streamline IT department productivity. By formalizing the structures that aid ongoing monitoring, IT departments can focus on proactively reviewing and collecting documentation rather than defensively responding to threats.
Moreover, assessments can help break down barriers. Starting with a security risk assessment puts corporate management and IT staff on the same page. Management needs to make decisions that mitigate risk while IT staff implements them. Working together from the same risk assessment gives everyone the information they need to protect the organization, and facilitates buy-in to security efforts beyond the IT department.
Enterprise security risk assessments also establish the basis for self-review. While IT staff knows the technical system, network, and application information, implementation depends on staff in other business units. Risk assessments provide accessible reports focused on actionable information, so that all involved can take the appropriate level of responsibility. To foster a culture of compliance, security cannot operate in isolation.
Finally, security risk assessments help share information across departments. With individualized vendors and systems, different departments within an organization may not know what others are doing. Since upper management within larger companies must all share responsibility, assessments provide the insight necessary for meaningful discussions supporting IT security.
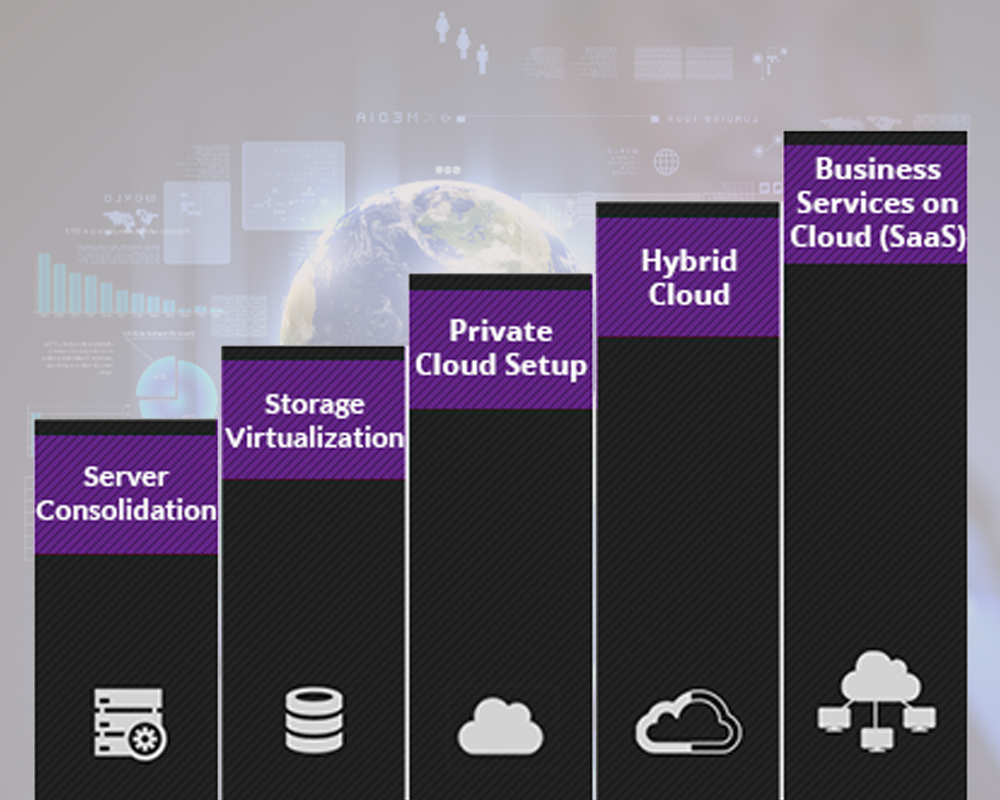
Cloud Consulting Services
Cloud Computing as a paradigm, is fundamentally altering the art and science of doing business online and represent a profound transformation in IT infrastructure. It enables the organizations to operate efficiently and provides scalability, responsiveness and drive growth and revenue.
We at GPC Tech Solutions - Dubai, work with our clients to assess the suitability for the cloud, help them choose the precise platforms and assist them put their best foot forward. Enabling our customers to analyze cloud readiness quotient and adopt cloud technologies through well-defined maturity models are our key strengths. We have a proven track record of successful IT implementations. We are now helping Qatar in Effective Utilization of Computing Resources, analyzing ROI on cloud adoption, reducing Data center Space Utilization, Centralized Management & Upgrades and Faster Deployments of solutions into Cloud etc. We give you the much-needed confidence by setting up a road map for managing successful cloud migration, development, integration and administration services through our cloud consulting services.
Unique Business Benefits That You Can Enjoy
Understand if you’re Cloud ready in primary stages.
Reduced software costs.
Simple scalability.
Improved operations & time for innovation.
Achieve seamless customization and automation of Cloud solutions.
Rapid deployment provider for all cloud services.
Reduced possibilities of complications and imbalances – we avoid dealing with several providers, technologies, apps, user provisioning, security, identity, etc.
Step-by-step implementation turns out to be much easier and swift – we understand your business better.
Creative
Technology
Branding & Promos
Value Added
GPC Tech Solutions Story
We’re GPC Tech Solutions, a leading branding & technology consulting agency from Dubai, UAE that believes in the power of the right message. Of building brands through clear, relevant, strategic communication. We work to motivate your target audience, not confuse them by camouflaging your brand with so-called creativity. That said, we love to push the envelope and create clutter breaking communication, wherever appropriate.
With years of collective team experience in Branding strategy, Design, Digital Marketing & Technology Consulting GPC Tech Solutions aims to help you achieve your goals.
Read more
Quick Links
Get in Touch
Green point computer, Al Fajer Complex
Dubai - United Arab Emirates (+971) 5681 89 455
sales@gpcsolutions.ae
(+971) 5681 89 455




